If you're an individual sharing your visiting cards with an unknown person or an entity putting out an advertisement for a job where it shares a lot of information about its operating systems, they're exposing themselves to hackers.
According to Terry Cutler, CEO of Cyology Labs and Ethical Hacking, when companies put out an advertisement to hire an individual, especially in the IT departments, they share details of the active systems that they operate. This exposes them to the risk of hacking because generally such advertisements contain good information that hackers use to break into the system.
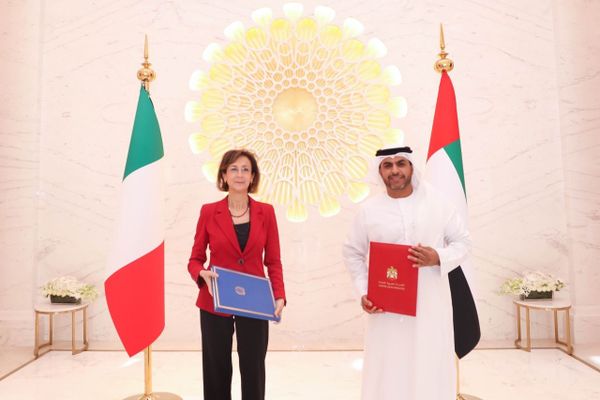
While speaking at a conference in Dubai on Wednesday, Cutler, who is voted No.1 top influencer in cybersecurity, noted that many people use very simple passwords such as adding 123 with their first, second or family names. Hence, when they share their visiting cards, they contain all the relevant information that hackers require to hack an individual's email or other personal information.
"A visiting card gives a ton of information – person's full name, his email address to phish in. It contains first and last names. And all the companies usually have a similar structure for emails and passwords; hence, hacking off one email makes it easier to hack others as well. Then there are open-source intelligence tools with whom they are linked and it helps to launch an efficient attack," he said.
"Another place that provides information to a hacker is job post. It helps hackers to know what the company's software is running, which systems are live and what vulnerabilities exist in the system."
He highlighted that there have been instances where the white hackers, or good hackers, found scanned passports with digital signatures and nude photos as well.
"I know what you did last summer," he said laughingly.
Assigned by companies, white hackers exploit computer systems or networks to identify their security flaws so they can make recommendations for improvement.
"Hackers want to know everything about you, using public sources like Google to build their battle plan. They want to find out who the company's vendors are, how many employees work in the company, who is CEO and where does CEO live and even to which school his kids go to," he said.
Cutler pointed out that sometimes executives use the same password for their personal and corporate emails, which can compromise both the email in case of breach of security of one email.
It's estimated that 95 per cent of large corporates are targeted by malicious traffic and it takes about 60 days on average to resolve a cyberattack, while 54 per cent of breaches remain undiscovered for months. Cybercrime is around a one trillion dollar industry, and it's estimated nearly every company has malware.
Small businesses, according to Cutler, are highly exposed to hacking because they think they are too small to be hacked and don't have the resources and technical know-how to stop cyberattacks.
Cutler added that employees are a major risk to the companies.
"Employees sometimes store on cloud data without IT department's knowledge. A lot of people bring personal computers also to the office to work on it. If employees don't understand the risk, the information will be misused, therefore it's important to create awareness among employees."
There are different ways to create unbreakable passwords.
Firstly, people can use upper case, lower case and symbols with 16 to 25-word-long passwords. It might be very difficult to type in but it's easy to remember.
"It's simple if you can think of phrases. For example, 'I had a great day at work in 2022'.
We can simply remove space and say I@had@a@great@day@at@work@in@2022.
" Then people can use two-step verification which is critically important if people want to protect their details," said Terry Cutler, CEO of Cyology Labs.
And if people want to know whether their email has been compromised, they can go to haveibeenpwned.com and find out.
News Source: Khaleej Times